- Why Crypto Wallet Security Can’t Be Ignored
- 10 Essential Practices to Guard Your Crypto Wallet Safely
- Advanced Protection Strategies
- FAQs: Guarding Crypto Wallets Safely
- What’s the most common crypto wallet vulnerability?
- How often should I check wallet security settings?
- Are mobile wallets safe for large amounts?
- Can stolen crypto be recovered?
- Should I use crypto wallet insurance?
Why Crypto Wallet Security Can’t Be Ignored
With over $3.8 billion stolen in crypto hacks during 2022 alone (Chainalysis report), securing digital assets has never been more critical. Your crypto wallet is the fortress protecting your financial future – but unlike traditional banks, you are solely responsible for its security. This guide delivers actionable best practices to guard your crypto wallet safely against hackers, scams, and human error. Implement these strategies to sleep soundly knowing your investments are protected.
10 Essential Practices to Guard Your Crypto Wallet Safely
- Use Hardware Wallets for Bulk Storage
Cold storage devices like Ledger or Trezor keep private keys offline, immune to online attacks. Reserve these for 90%+ of your holdings – they’re the digital equivalent of bank vaults.
- Create Uncrackable Passwords & Passphrases
Generate 12+ character passwords mixing uppercase, symbols, and numbers. Never reuse passwords across platforms. Consider diceware passphrases like ‘coral-breeze-7-pixel-verify’ for better memorability.
- Enable Multi-Factor Authentication (2FA)
Always activate 2FA using authenticator apps (Google/Microsoft Authenticator) – never SMS. This adds a critical second layer beyond passwords.
- Verify All Wallet Addresses Manually
Malware can alter copied addresses. Always verify the first/last 4 characters of recipient addresses before sending transactions.
- Maintain Air-Gapped Backups
Store encrypted seed phrases on metal plates (not paper!) in geographically separate locations. Never digitize or photograph recovery phrases.
- Update Software Immediately
Wallet apps and OS updates often patch critical vulnerabilities. Enable auto-updates where possible.
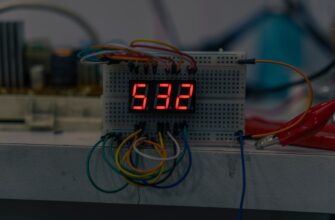
- Use Dedicated Security Devices
Operate crypto wallets only on malware-free devices separate from daily browsing. $100 dedicated smartphones prevent most phishing risks.
- Beware of Phishing Traps
Scammers impersonate wallet support teams. Never share seeds or keys – legitimate services will never ask for them.
- Limit Smart Contract Permissions
Revoke unnecessary token approvals monthly using tools like Etherscan’s Token Approvals checker to prevent drainer attacks.
- Employ Multi-Signature Wallets
Require 2-3 approvals for transactions (e.g., one device + biometric). Ideal for family or business wallets.
Advanced Protection Strategies
Beyond the fundamentals, consider these enhanced measures: Use VPNs on public Wi-Fi, whitelist withdrawal addresses on exchanges, and segment assets across multiple wallets. Regularly simulate recovery processes to ensure backup integrity. Remember: complexity equals security in the crypto realm.
FAQs: Guarding Crypto Wallets Safely
What’s the most common crypto wallet vulnerability?
Human error causes 95%+ of losses – especially seed phrase mismanagement and phishing scams. Technical hacks represent less than 5% of incidents.
How often should I check wallet security settings?
Audit permissions monthly, check software updates weekly, and verify backup accessibility quarterly. Treat security like dental hygiene – consistent small efforts prevent disasters.
Are mobile wallets safe for large amounts?
Only for small, transactional sums (<5% portfolio). Use hardware wallets for primary storage. Mobile wallets risk SIM-swapping, malware, and physical theft.
Can stolen crypto be recovered?
Typically no – blockchain transactions are irreversible. Some centralized exchanges may freeze stolen funds if reported immediately, but success rates are low. Prevention is paramount.
Should I use crypto wallet insurance?
Services like Coinbase Custody or Ledger Donjon offer insurance, but premiums are high. Self-custody with rigorous practices remains the most reliable protection for most users.